Overview
In the first week of May 2026, Cisco Systems disclosed and patched a set of critical vulnerabilities affecting its IOS XE software platform — the operating system powering a vast share of enterprise routers, switches, and wireless controllers deployed globally. The flaws, tracked under multiple CVEs, carry CVSS scores as high as 9.8, placing them in the critical severity tier. Security researchers and government cybersecurity agencies across North America, Europe, and Asia-Pacific issued coordinated advisories urging immediate remediation.
The Vulnerabilities Explained
The disclosed vulnerabilities span three primary attack vectors:
- Unauthenticated Remote Code Execution (RCE): An attacker with network access to the device's web UI can execute arbitrary code without credentials, potentially gaining full administrative control.
- Privilege Escalation via REST API: A logic flaw in the IOS XE REST API allows low-privilege authenticated users to elevate permissions to root level.
- Denial-of-Service (DoS) via Crafted Packets: Specially crafted OSPF or BGP packets can trigger an unexpected device reload, disrupting routing operations in enterprise and carrier networks.
The RCE vulnerability is considered the most severe, as it requires no authentication and can be exploited remotely over the internet if the web management interface is exposed.
Affected Devices and Scope
| Device Category | Affected IOS XE Versions | Severity |
|---|---|---|
| Catalyst 9000 Series Switches | 17.x prior to 17.12.4 | Critical (CVSS 9.8) |
| ASR 1000 Series Routers | 17.x prior to 17.12.4 | Critical (CVSS 9.8) |
| ISR 4000 Series Routers | 16.x, 17.x prior to patch | High (CVSS 8.6) |
| Catalyst 8000 Edge Platforms | 17.x prior to 17.12.4 | Critical (CVSS 9.8) |
| Wireless LAN Controllers (WLC) | 17.x prior to 17.12.3a | High (CVSS 7.5) |
Cisco estimates tens of thousands of internet-facing devices remain unpatched as of the disclosure date, with Shodan scans revealing a significant number of management interfaces exposed to the public internet.
Cisco's Response and Patch Details
Cisco's Product Security Incident Response Team (PSIRT) published the advisories on May 7, 2026, alongside immediate availability of fixed software releases. The company credited both internal discovery and responsible disclosure from third-party security researchers for identifying the flaws. Key patch releases include:
- IOS XE 17.12.4: Addresses all three critical and high CVEs for Catalyst and ASR platforms.
- IOS XE 17.12.3a: Targeted fix for the WLC DoS vulnerability.
- Interim workarounds: Cisco recommends disabling the HTTP/HTTPS web management interface on internet-facing devices where patching cannot be applied immediately, using the commands
no ip http serverandno ip http secure-server.
Cisco confirmed no active exploitation in the wild had been observed at the time of publication but warned that proof-of-concept exploit code is likely to emerge rapidly given the public nature of the disclosure.
Global Infrastructure Impact
IOS XE devices underpin critical infrastructure worldwide — from enterprise campus networks and data centers to internet service providers and government networks. The scale of potential exposure has prompted responses from multiple national cybersecurity bodies:
- CISA (USA): Added the RCE vulnerability to its Known Exploited Vulnerabilities catalog with a remediation deadline of May 21, 2026, for federal agencies.
- NCSC (UK): Issued a technical alert and urged all Critical National Infrastructure operators to audit exposure immediately.
- ENISA (EU): Circulated an early warning bulletin to EU member state CERTs.
- ACSC (Australia): Published an advisory targeting financial services and healthcare sectors with high concentrations of Cisco infrastructure.
Telecom carriers in Asia-Pacific, particularly in Japan, South Korea, and Singapore, reported accelerated patch deployment windows in coordination with Cisco's regional support teams.
Recommended Actions for IT Teams
- Audit inventory immediately: Identify all IOS XE devices in your environment and confirm software versions using
show version. - Prioritize internet-facing devices: Any device with the web UI exposed externally is at the highest risk and must be patched or mitigated first.
- Apply patches: Upgrade to IOS XE 17.12.4 or the relevant fixed release for your platform as documented in Cisco's advisory.
- Apply workarounds where patching is delayed: Disable the HTTP/HTTPS server interface and restrict management access via ACLs.
- Monitor for indicators of compromise: Review logs for unexpected privilege escalations, unusual API calls, or spontaneous device reloads.
- Enable Cisco's automated advisories: Subscribe to Cisco PSIRT notifications to reduce response lag for future disclosures.
Why This Matters for Networking Professionals
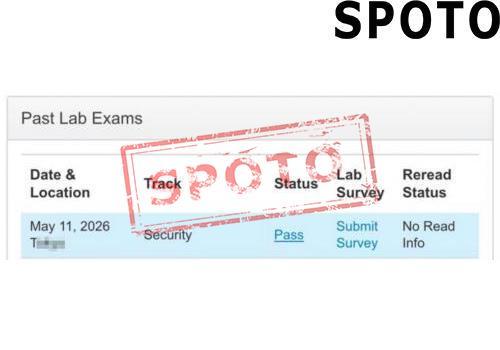
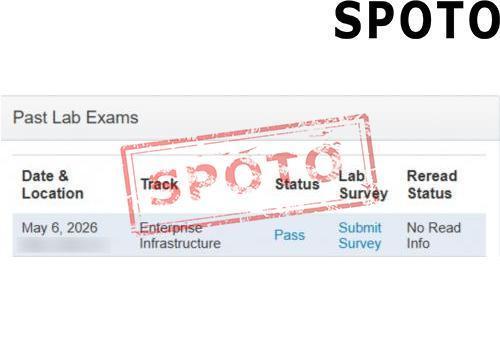
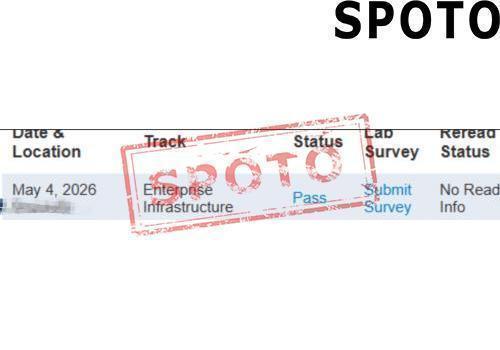
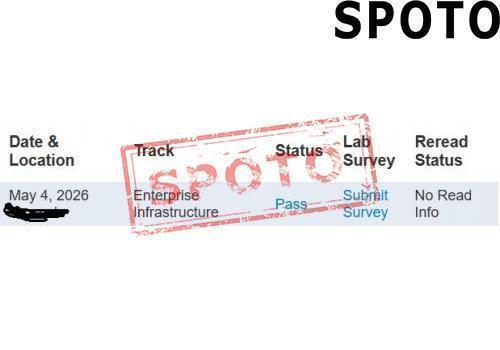
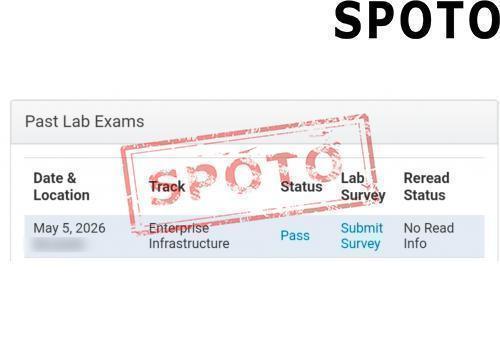
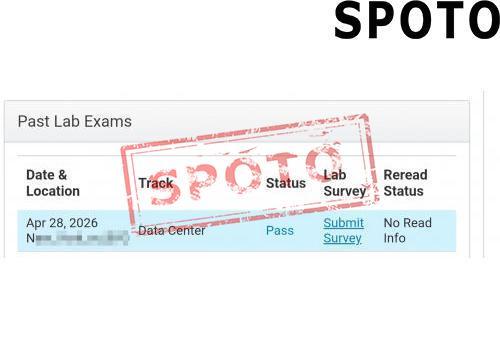
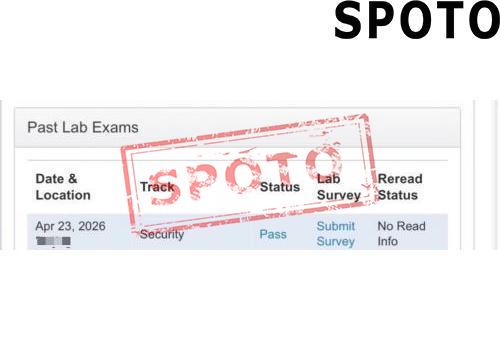
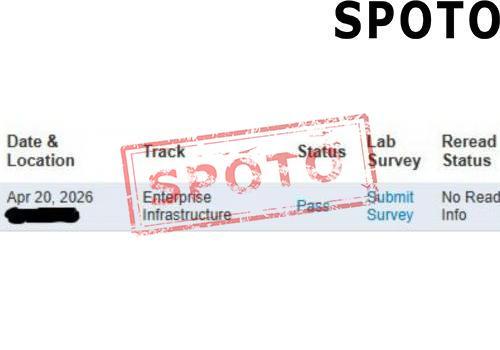
For IT professionals pursuing Cisco certifications — including CCNA, CCNP, and CCIE — this incident is a real-world demonstration of core exam domains: network security hardening, IOS software lifecycle management, vulnerability assessment, and incident response. Understanding IOS XE architecture, the role of the web management interface, and ACL-based access control are all subjects tested across Cisco's certification tracks. Platforms such as SPOTO's IT certification exam training offer up-to-date practice materials aligned with the latest Cisco exam blueprints, helping candidates build both theoretical knowledge and practical skills needed to manage and secure enterprise infrastructure of exactly this type.
Sources
- Cisco Security Advisories — Cisco PSIRT Official Publications (May 2026)
- CISA Known Exploited Vulnerabilities Catalog — IOS XE RCE Entry (May 2026)
- NCSC UK — Technical Alert: Cisco IOS XE Critical Vulnerabilities (May 2026)
- ENISA Early Warning Bulletin — Cisco IOS XE Vulnerabilities (May 2026)
- Australian Cyber Security Centre (ACSC) — Advisory on Cisco IOS XE (May 2026)
- SPOTO IT Certification Exam Training — Cisco CCNA, CCNP, CCIE Resources
- Global Network Communications Market 2026: AI-Driven 5G Advanced Deployments Accelerate Amid New Spectrum Policy Shifts
- Cisco Warns of Critical IOS XE Vulnerability Actively Exploited in Global Networking Infrastructure Attacks (April 2026)
- Wi-Fi 7 Adoption Surges Globally as Enterprises Race to Upgrade Network Infrastructure in 2026
- Cisco Unveils Next-Gen AI-Powered Networking Platform at Cisco Live 2026: What IT Pros Need to Know
- Wi-Fi 7 Mass Deployment Accelerates in 2026 as Global Enterprises and Carriers Race to Upgrade Network Infrastructure