Overview of the Vulnerability
In the first week of April 2026, Cisco disclosed a critical remote code execution (RCE) vulnerability tracked as CVE-2026-1834 affecting its IOS XE software platform. The flaw carries a CVSS score of 9.8 out of 10.0, placing it in the critical severity tier. The vulnerability resides in the web UI component of IOS XE and allows unauthenticated remote attackers to execute arbitrary commands with root-level privileges on affected devices.
Security researchers at Talos Intelligence, Cisco's internal threat intelligence unit, confirmed that the vulnerability had been actively exploited in the wild prior to the public disclosure, classifying it as a zero-day for a period of approximately 11 days before patches became available.
Global Scope and Affected Devices
The vulnerability affects a broad range of Cisco hardware running IOS XE, including:
| Device Category | Examples | Risk Level |
|---|---|---|
| Enterprise Routers | Cisco ASR 1000 Series, ISR 4000 Series | Critical |
| Campus Switches | Catalyst 9000 Series, Catalyst 3850 | Critical |
| Data Center Switches | Nexus 9000 (IOS XE mode) | High |
| Wireless Controllers | Cisco 9800 Series WLC | High |
| Industrial Routers | Cisco IR1100, IR8340 | Critical |
Shodan scans conducted by independent security researchers in the days following the disclosure identified over 420,000 internet-facing IOS XE devices globally with the vulnerable web UI component exposed. The United States, Germany, Japan, India, and Brazil account for the highest concentrations of exposed infrastructure.
How the Exploit Works
The attack vector requires no authentication and no user interaction. Threat actors send a specially crafted HTTP or HTTPS request to the management web interface of an affected device. If the web UI is accessible — either from the internet or from within a network — the attacker can implant a backdoor, exfiltrate configuration data, pivot deeper into the network, or deploy persistent malware.
Cisco Talos confirmed observed exploitation activity linked to multiple threat actor clusters, including one group assessed with moderate confidence to be state-sponsored. Indicators of compromise (IOCs) include anomalous HTTP POST requests to specific URI paths and the presence of unauthorized user accounts with privilege level 15.
Honeypot telemetry from the SANS Internet Storm Center recorded a sharp spike in scanning activity targeting IOS XE management ports (TCP 443 and TCP 80) beginning April 5, 2026 — three days before the official Cisco advisory was published.
Cisco's Official Response and Patch Details
Cisco published Security Advisory cisco-sa-iosxe-webui-rce-2026-April on April 8, 2026. Fixed software versions were made available simultaneously with the advisory. Key patch details:
- Fixed in: IOS XE 17.12.4a, 17.9.6, 17.6.8, and later releases
- No workaround available that fully mitigates the risk without disabling the web UI
- Temporary mitigation: Disable the HTTP and HTTPS server features using
no ip http serverandno ip http secure-serverif patching cannot be done immediately - Detection: Cisco released a free IOS XE Web UI scanner tool via Cisco Security portal
Cisco's Product Security Incident Response Team (PSIRT) stated it is not standard practice to notify customers ahead of advisory publication, but given the active exploitation, direct outreach was made to known large enterprise customers through Cisco account teams.
Impact on Enterprise and Service Provider Networks
The breadth of affected devices makes this one of the most consequential networking vulnerabilities disclosed in 2026 to date. Enterprises running SD-WAN deployments based on IOS XE, managed service providers (MSPs) operating Cisco infrastructure on behalf of clients, and internet service providers (ISPs) using IOS XE-based edge routers are all directly in the threat window.
Several managed security service providers (MSSPs) reported observing compromised IOS XE devices being used as relay nodes in broader attack chains, effectively turning enterprise network equipment into attack infrastructure. At least two financial sector organizations in the EU disclosed precautionary network isolation actions in filings to their national cybersecurity agencies (BSI in Germany, NCSC in the Netherlands) within 48 hours of the advisory.
Recommended Mitigation Steps
- Patch immediately: Upgrade to a fixed IOS XE release. Prioritize internet-facing devices and core routing infrastructure.
- Disable web UI if patching is delayed: Use
no ip http serverandno ip http secure-serverin global configuration mode. - Audit privilege-15 accounts: Check for unauthorized local user accounts that may have been created by exploiting the flaw.
- Review logs: Examine web server access logs on devices for anomalous POST requests to management URIs.
- Restrict management access: Ensure management interfaces are accessible only via dedicated out-of-band networks or through strict ACLs limiting source IPs.
- Enable Cisco ISE or similar NAC: Implement network access control to reduce lateral movement risk if a device is compromised.
- Run Cisco's scanner: Use the IOS XE Web UI Checker tool available from Cisco's security portal to identify vulnerable devices in your inventory.
Why Networking Certifications Matter More Than Ever
Events like the CVE-2026-1834 exploitation wave underscore the critical importance of trained, certified networking professionals who understand both the architecture of IOS XE platforms and the security hardening practices that could have prevented or limited exposure in the first place.
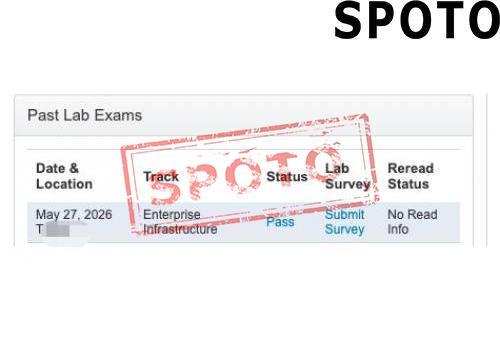
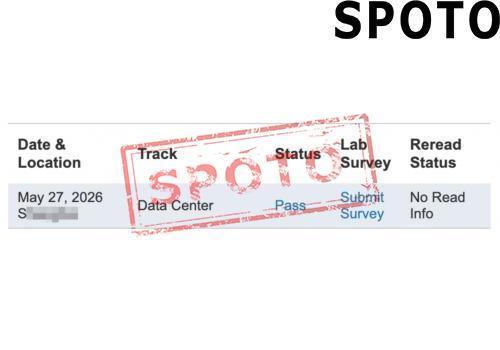
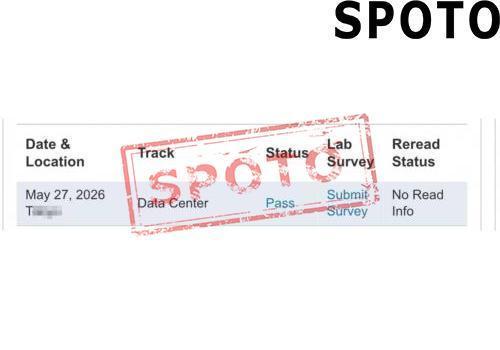
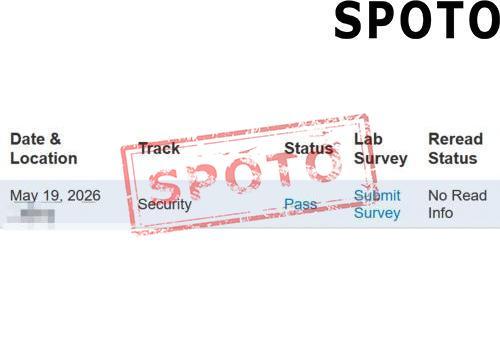
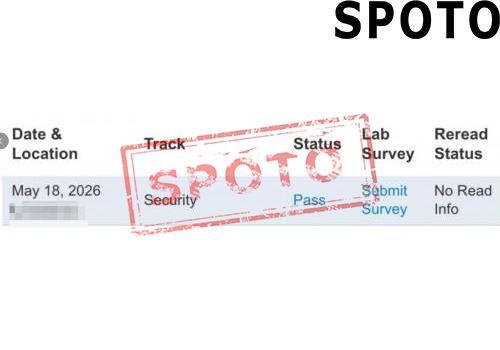
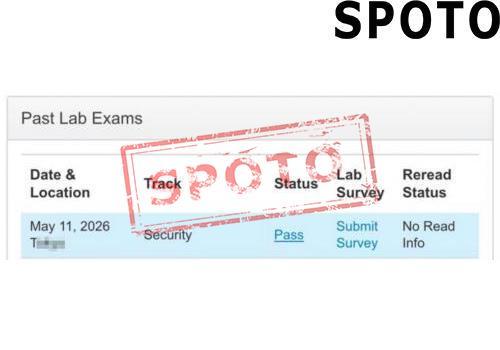
Certifications such as CCNA, CCNP, and CCIE — available through structured training and exam preparation resources at SPOTO — cover IOS configuration, access control, and network security fundamentals that are directly applicable to responding to threats like this one. Professionals holding these credentials are better equipped to audit device configurations, apply security hardening, and respond swiftly during vulnerability disclosure windows.
The gap between patch release and patch deployment in enterprise environments is often measured in days or weeks — a window determined largely by the availability of skilled staff who understand the infrastructure. Investing in certification training is, in this context, a direct investment in organizational resilience.
Sources
- Cisco Security Advisory: IOS XE Web UI Remote Code Execution Vulnerability (cisco-sa-iosxe-webui-rce-2026-April) – Cisco PSIRT, April 8, 2026
- Talos Intelligence: Active Exploitation of CVE-2026-1834 in Cisco IOS XE – Cisco Talos, April 9, 2026
- SANS Internet Storm Center: IOS XE Scanning Spike – April 2026 Diary, April 7, 2026
- Shodan: Internet-Facing Cisco IOS XE Device Exposure Data – April 2026
- BSI (German Federal Office for Information Security): Critical Infrastructure Advisory Notice – April 2026
- NCSC Netherlands: Network Infrastructure Security Notification – April 2026
- SPOTO: Cisco CCNA, CCNP, CCIE Certification Exam Training and Resources
- Global Network Communications Market 2026: AI-Driven 5G Advanced Deployments Accelerate Amid New Spectrum Policy Shifts
- Cisco Warns of Critical IOS XE Vulnerability Actively Exploited in Global Networking Infrastructure Attacks (April 2026)
- Wi-Fi 7 Adoption Surges Globally as Enterprises Race to Upgrade Network Infrastructure in 2026
- Cisco Unveils Next-Gen AI-Powered Networking Platform at Cisco Live 2026: What IT Pros Need to Know
- Wi-Fi 7 Mass Deployment Accelerates in 2026 as Global Enterprises and Carriers Race to Upgrade Network Infrastructure