CCIE Security Lab Exam Dump List
-
Luc***2026/06/05order CCIE ***Hen***2026/06/05order CCIE ***Ale***2026/06/05order CCIE ***
-
Mas***2026/06/05order CCIE ***Mic***2026/06/05order CCIE ***Eth***2026/06/05order CCIE ***
-
Dan***2026/06/05order CCIE ***Jac***2026/06/05order CCIE ***Log***2026/06/05order CCIE ***
-
Jac***2026/06/05order CCIE ***Lev***2026/06/05order CCIE ***Seb***2026/06/05order CCIE ***
-
Mat***2026/06/05order CCIE ***Jac***2026/06/05order CCIE ***Owe***2026/06/05order CCIE ***
-
The***2026/06/05order CCIE ***Aid***2026/06/05order CCIE ***Sam***2026/06/05order CCIE ***
-
Lia***2026/06/05order CCIE ***Noa***2026/06/05order CCIE ***Oli***2026/06/05order CCIE ***
-
Eli***2026/06/05order CCIE ***Wil***2026/06/05order CCIE ***Jam***2026/06/05order CCIE ***
-
Luc***2026/06/05order CCIE ***
-
Mas***2026/06/05order CCIE ***
-
Dan***2026/06/05order CCIE ***
-
Jac***2026/06/05order CCIE ***
-
Owe***2026/06/05order CCIE ***
-
The***2026/06/05order CCIE ***
-
Lia***2026/06/05order CCIE ***
-
Wil***2026/06/05order CCIE ***
CCIE Security Lab Exam Info-Fully Prepare Exam With SPOTO
The Cisco CCIE Security (v6.1) Practical Exam is an eight-hour, hands-on exam that requires a candidate to plan, design, deploy, operate, and optimize network security solutions to protect your network. CCIE Security LAB Exam include 2 models (Design and Deploy & Operate & Optimize). You should know essential knowledge on Complex security. SPOTO offers latest & updated CCIE Security Lab Exam Workbook and Solutions for candidates to fully prepare CCIE Security Lab exam with ease. You can pass your CCIE Security Lab exam in the first attempt by using SPOTO CCIE Security Lab study materials if you work hard and practice more.

CCIE Security Lab
hands-on exam
1,600 $ USD
hands-on exam
8 hours
3 years
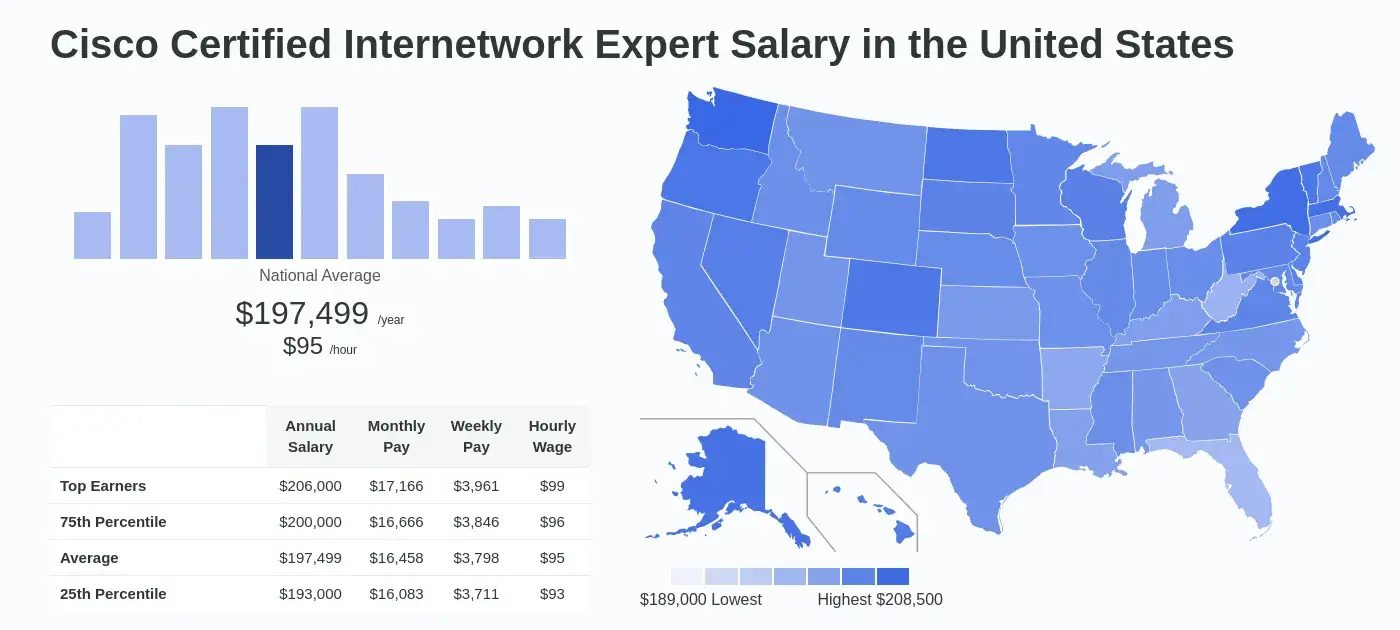
Salary and Job Opportunities:
While ZipRecruiter is seeing annual salaries as high as $212,500 and as low as $42,000, the majority of CCIE salaries currently range between $125,000 (25th percentile) to $173,500 (75th percentile) with top earners (90th percentile) making $193,500 annually across the United States. The average pay range for a CCIE varies greatly (by as much as $48,500), which suggests there may be many opportunities for advancement and increased pay based on skill level, location and years of experience.Job Title 1.Network Engineer CCIE
2.CCIE Architect
3.CCIE Engineer
4.CCIE Cisco
5.CCIE Cloud
The Cisco CCIE Security (v6.1) Practical Exam is an eight-hour, hands-on exam that requires a candidate to plan, design, deploy, operate, and optimize network security solutions to protect your network. CCIE Security LAB Exam include 2 models (Design and Deploy & Operate & Optimize). You should know essential knowledge on Complex security. SPOTO offers latest & updated CCIE Security Lab Exam Workbook and Solutions for candidates to fully prepare CCIE Security Lab exam with ease. You can pass your CCIE Security Lab exam in the first attempt by using SPOTO CCIE Security Lab study materials if you work hard and practice more.

CCIE Security Lab
hands-on exam
1,600 $ USD
hands-on exam
8 hours
3 years
Salary and Job Opportunities:
While ZipRecruiter is seeing annual salaries as high as $212,500 and as low as $42,000, the majority of CCIE salaries currently range between $125,000 (25th percentile) to $173,500 (75th percentile) with top earners (90th percentile) making $193,500 annually across the United States. The average pay range for a CCIE varies greatly (by as much as $48,500), which suggests there may be many opportunities for advancement and increased pay based on skill level, location and years of experience.Job Title 1.Network Engineer CCIE
2.CCIE Architect
3.CCIE Engineer
4.CCIE Cisco
5.CCIE Cloud
About CCIE Sec Lab Exam
1.CCIE Security Lab v6.1
On February 24, 2020, Cisco implemented several changes in its certification programs to meet the demands of fast-changing technologies. The latest CCIE certification requires a candidate to pass a core exam and a concentration exam. The core exam is the same for CCNP and CCIE candidates. Nevertheless, they can choose a concentration area. If you want to get a certification for CCIE Security, you must take the CCIE Security lab exam after passing the core exam.
The CCIE Security certification is designed to help you become a technical leader in the ever-changing world of security technologies and solutions. Passing the CCIE sec lab exam validates your knowledge and skills in planning, designing, operating, and optimizing end-to-end complex technologies and solutions.
The new CCIE Security lab exam, minor revision 6.1, was published in October 2023. You can consult our customer service to get the latest exam solutions! Or continue reading point 2.
2.CCIE Security Lab v6.1 Study Plan
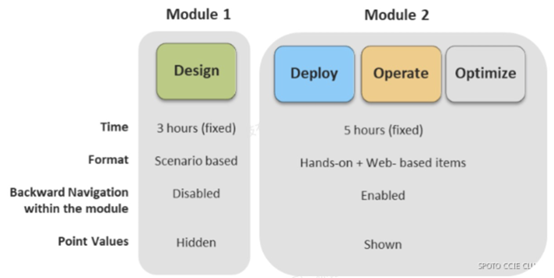
CCIE Security LAB Exam include 2 models (Design and Deploy & Operate & Optimize).
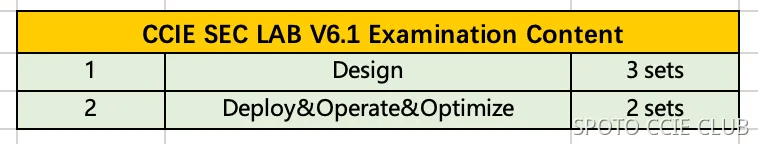
This is the material content that you need practice. You will face them when you take the exam.
Design: 3 sets
Deploy & Operate & Optimize: 2 sets
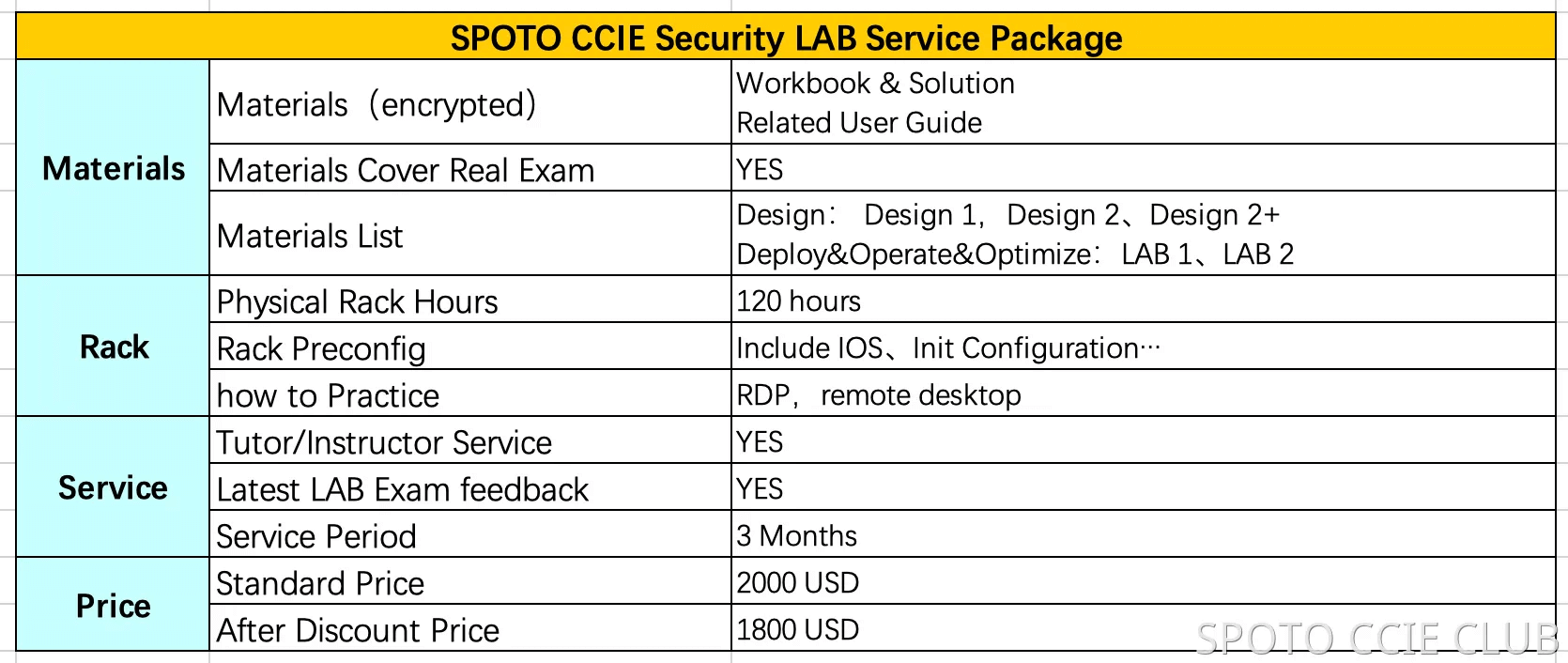
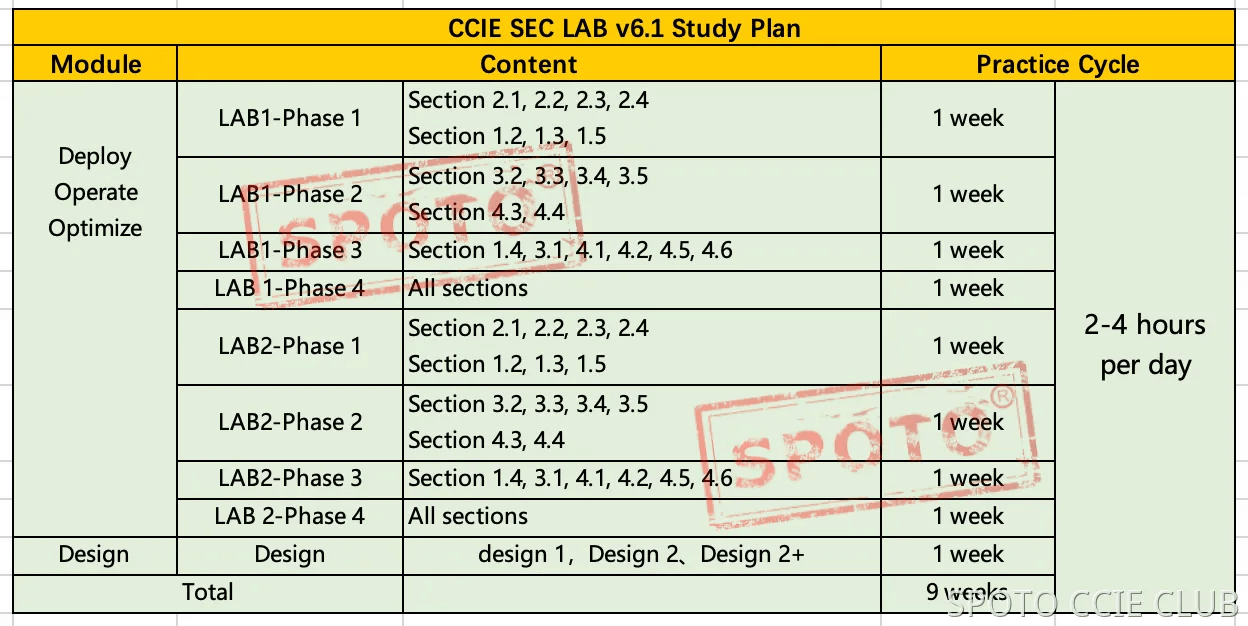
This is the CCIE Security v6.1 LAB study plan we suggest.
If you can spend 2~4 hours on lab practice per day, you can take the exam after 9 weeks.
We provide 3 months service time, you can follow your schedule to practice, it is flexible.
We delivered the materials stage by stage:
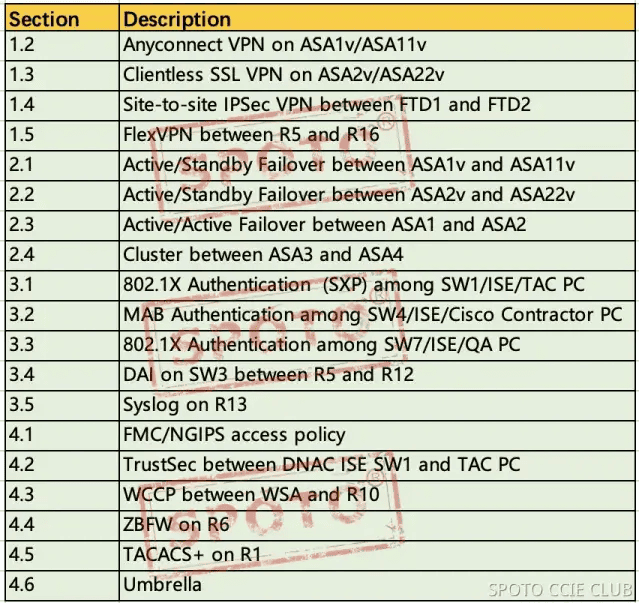
LAB1 - Phase 1:Section 2.1, 2.2, 2.3, 2.4 and Section 1.2, 1.3, 1.5
LAB1 - Phase 2:Section 3.2, 3.3, 3.4, 3.5 and Section 4.3, 4.4
LAB1 - Phase 3:Section 1.4, 3.1, 4.1, 4.2, 4.5, 4.6
LAB1 - Phase 4:All Section
LAB2 - Phase 1:Section 2.1, 2.2, 2.3, 2.4 and Section 1.2, 1.3, 1.5
LAB2 - Phase 2:Section 3.2, 3.3, 3.4, 3.5 and Section 4.3, 4.4
LAB2 - Phase 3:Section 1.4, 3.1, 4.1, 4.2, 4.5, 4.6
LAB2 - Phase 4:All Section
We delivered Phase 2 materials after you complete Phase 1.
We delivered Phase 3 materials after you complete Phase 2.
The design materials will be sent 1 week before your exam date.
3.Workbook Demo
Here is a CCIE Security Design resources question demo:
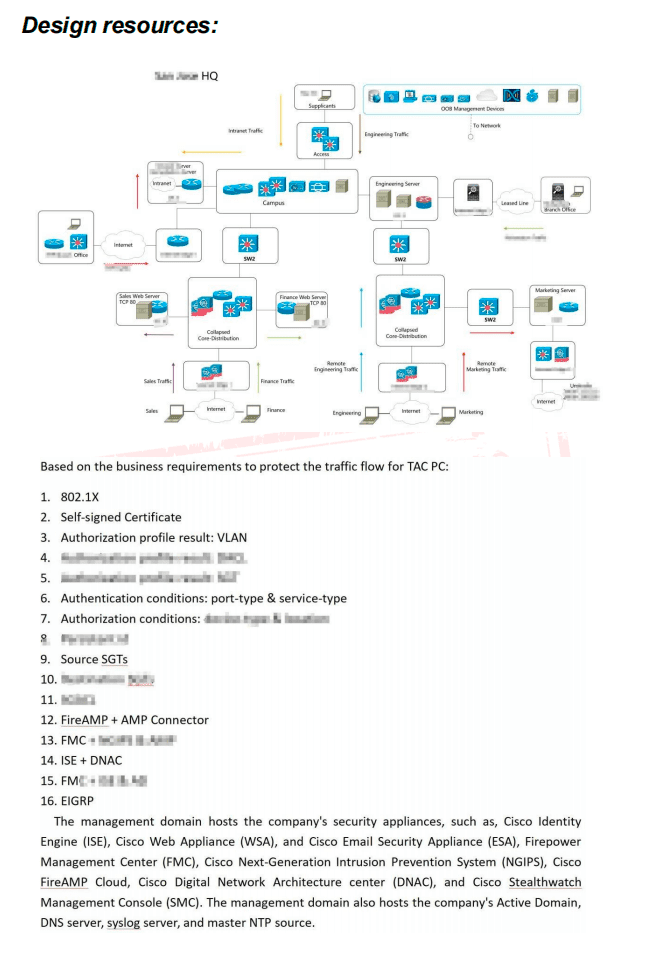
4.About the CCIE Security Lab v6.1 Exam
The Cisco CCIE Security (v6.1) Practical Exam is an eight-hour, hands-on exam that requires a candidate to plan, design, deploy, operate, and optimize network security solutions to protect your network. The exam costs $1,600.
5.Major topics of CCIE Security Lab v6.1 Exam:
1. Perimeter Security and Intrusion Prevention (20%)
2. Secure Connectivity and Segmentation (20%)
3. Infrastructure Security (15%)
4. Identity Management, Information Exchange, and Access Control (25%)
5. Advanced Threat Protection and Content Security (20%)
6.Benefits of Passing the CCIE Security Lab v6.1 Exam
The CCIE Security certification is one of the certifications given by Cisco to IT professionals that pass the core exam and the CCIE Security lab exam. You need to invest time, money, and effort to get the badge, but you will enjoy several benefits as follows:
High Salary
Having a CCIE Security certification will entitle you to a high salary. This certification is considered one of the highest-paid IT certifications in the world. In the year 2020, a CCIE Security badge holder earns an average annual salary of $126,000. The world needs more than 200,000 CCIE Security certification holders while there are only 6,000 CCIE Security certified worldwide.
Increased job opportunities
Once you are already a CCIE Security certificate holder, a lot of jobs await you. You can be Network Administrator, Network Security Engineer, Network Security Administrator, and Network Security Specialist. You will find it fast and easy to get a job anywhere in the world.
Career growth opportunities
With very few CCIE Security certification holders, you will have a big chance to get promoted to top positions. Employers will offer attractive salary and benefits packages to convince you to work in their company.
7.How to Pass the CCIE Security Lab v6.1 Exam on the First Try?
Although the CCIE Security lab exam is one of the toughest Cisco certifications exams, there is a way of cracking it and passing on the first try. Get the CCIE security lab exam dumps and have a 100% chance of passing the test the first time you take it. The dumps have been updated following the latest version. Register for our online certification course in the CCIE Security lab and receive videos, workbooks, and other study materials for the lab exam. . Our expert trainers will show you how hand-on experiments are done and explain well the workbook and solution.
Our CCIE security lab dumps are 100% real, valid, and updated to guarantee a 100% passing rate. SPOTO has been the leader in providing online certification training courses since 2003. We have produced thousands of certification exam passers in the last 18 years.
8.What is CCIE Security Certification?
The CCIE Security Certification refers to a credentialing program designed to validate the skills and knowledge of professionals in cybersecurity.
Inside Our CCIE Lab Infrastructure and Rack Environment
Conquer the CCIE SP exam with CCIE SP Lab v5.1 Demo
SPOTO provides the newest CCIE SP Lab v5.1 Demo, boost your success with our expertly crafted study materials for the newly updated Cisco CCIE SP exam. Dramatically increase your pass rate, and conquer the CCIE challenge.
Latest Passing Reports from SPOTO Candidates
Success Stories World's Online CCIE Security Lab Dump
RELATED Practice test
How Much Can You Make with the Certification?
Certified professionals can earn up to 40-percent more than their non-certified peers.
FAQ
1.What are the CCIE Security lab exam learning materials?
Software and setup instructions
Learning Materials, including Workbook, Solutions and Instruction Video.
Study Plan
The materials we provide by module delivery. We send CFG for practice first, we will send TS materials after you complete CFG practice. Finally is DIAG materials.
We reserve the rights to terminate all the services in case we learned you have been sharing our materials with others. Thank you for your understanding.



Success Stories World's Online CCIE Security Lab Dump