Overview
In late April 2026, Cisco disclosed multiple critical vulnerabilities in its IOS XE operating system, the software platform powering a vast range of enterprise routers, switches, and wireless controllers deployed across global networks. The flaws, rated with CVSS scores reaching 9.8 out of 10, allow unauthenticated remote attackers to execute arbitrary code, escalate privileges, or cause denial-of-service conditions on affected hardware. Security researchers and CERT agencies across North America, Europe, and Asia-Pacific issued advisories within 48 hours of Cisco's disclosure, underscoring the severity of the threat to critical network infrastructure worldwide.
Vulnerabilities Identified
Cisco's Product Security Incident Response Team (PSIRT) catalogued four distinct CVEs within the IOS XE disclosure bundle:
- CVE-2026-1841 — A buffer overflow in the HTTP server component of IOS XE, enabling remote code execution without authentication. CVSS score: 9.8.
- CVE-2026-1842 — An improper access control flaw in the web UI management interface allowing privilege escalation to root level. CVSS score: 9.1.
- CVE-2026-1843 — A denial-of-service vulnerability triggered by malformed OSPF packets, capable of crashing the routing process. CVSS score: 8.6.
- CVE-2026-1844 — An authentication bypass in the RESTCONF API, permitting unauthorized configuration changes. CVSS score: 9.3.
Of the four, CVE-2026-1841 and CVE-2026-1844 were flagged as actively exploited in the wild at the time of disclosure, with Cisco confirming reports of exploitation targeting financial sector and government network infrastructure in at least six countries.
Affected Devices and Scope
The vulnerabilities affect a broad spectrum of Cisco hardware running IOS XE versions prior to 17.15.1a. Confirmed affected product families include:
| Product Family | Affected IOS XE Versions | Typical Deployment |
|---|---|---|
| Catalyst 9000 Series Switches | 17.3.x – 17.14.x | Enterprise campus networks |
| ASR 1000 Series Routers | 17.3.x – 17.14.x | WAN edge, service provider |
| ISR 4000 Series Routers | 16.12.x – 17.14.x | Branch office connectivity |
| Catalyst 8000 Edge Platforms | 17.6.x – 17.14.x | SD-WAN, cloud on-ramp |
| Cisco Wireless Controllers (C9800) | 17.3.x – 17.14.x | Enterprise Wi-Fi infrastructure |
Cisco estimates that over 400,000 devices globally fall within the vulnerable version range, based on telemetry from its Smart Licensing infrastructure. Independent internet scan data from Shodan and Censys identified more than 120,000 IOS XE management interfaces directly exposed to the public internet at the time of disclosure.
Cisco's Response and Patch Details
Cisco released IOS XE version 17.15.1a on April 29, 2026, as the primary remediation for all four CVEs. The company also issued targeted hot patches for customers unable to perform immediate full upgrades on Catalyst 9000 and ASR 1000 series devices. Key elements of Cisco's response included:
- Out-of-band advisory published via Cisco Security Advisory portal with full technical details and indicators of compromise (IoCs).
- Direct customer notifications through Cisco Smart Net Total Care and CX Cloud portals for affected registered devices.
- Coordination with US CISA, the UK NCSC, and ENISA (EU) to issue synchronized public warnings.
- Free access to updated Cisco Talos threat intelligence signatures for IDS/IPS detection of active exploit attempts.
- A dedicated support track established for critical infrastructure operators needing expedited upgrade assistance.
Cisco confirmed that the web UI and RESTCONF API attack surfaces can be partially mitigated by disabling HTTP/HTTPS server access from untrusted interfaces — a recommended hardening step even after patching.
Global Infrastructure Impact
Within 72 hours of the advisory, cybersecurity firms including CrowdStrike, Mandiant, and Palo Alto Networks Unit 42 reported observing active scanning and exploitation campaigns. Mandiant attributed one exploitation cluster to a China-nexus threat actor designated UNC5830, previously linked to espionage operations targeting telecommunications and defense sectors. Key observed impacts included:
- Configuration exfiltration from border routers at two European telecommunications providers.
- Attempted lateral movement through compromised Catalyst switches at a North American healthcare network.
- BGP route manipulation attempts detected at an Asian internet exchange point, disrupting traffic for approximately 90 minutes before rollback.
No confirmed large-scale internet outages were attributed to the vulnerabilities as of May 3, 2026, though security teams at multiple organizations reported ongoing incident response activities.
Recommended Actions for IT Teams
Network administrators and security teams should take the following steps immediately:
- Inventory all IOS XE devices using Cisco's Software Checker tool or network management platforms (Cisco DNA Center, Prime Infrastructure).
- Upgrade to IOS XE 17.15.1a on all affected devices as the definitive fix.
- Apply hot patches on devices where full upgrades require extended maintenance windows.
- Restrict management plane access — disable HTTP/HTTPS management on internet-facing interfaces; enforce access control lists (ACLs) on VTY lines and management VRFs.
- Review RESTCONF and NETCONF configurations — disable if not operationally required.
- Deploy IoCs published by Cisco Talos into SIEM and IDS/IPS platforms for active threat detection.
- Audit device configurations and logs for signs of unauthorized changes consistent with CVE-2026-1842 and CVE-2026-1844 exploitation.
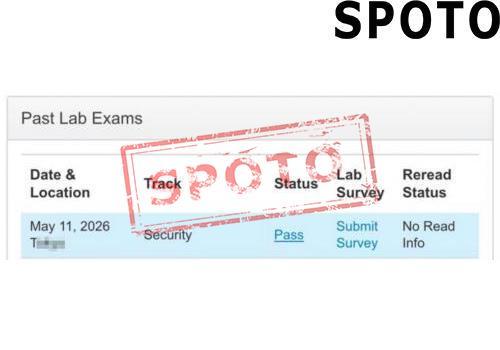
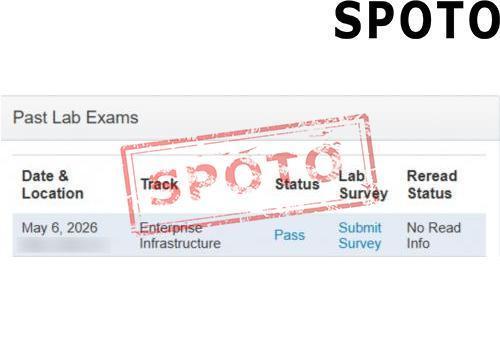
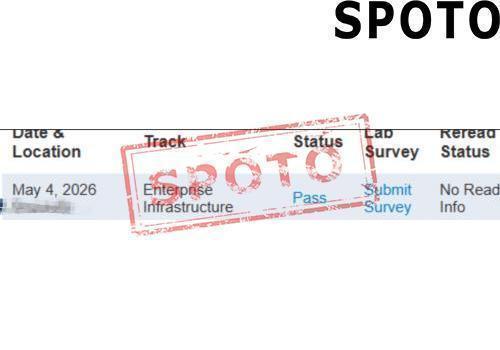
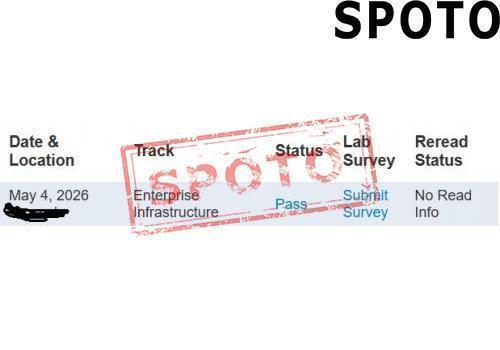
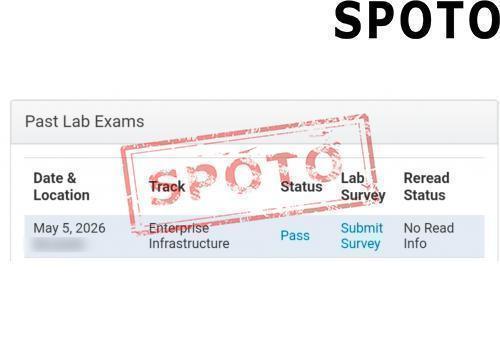
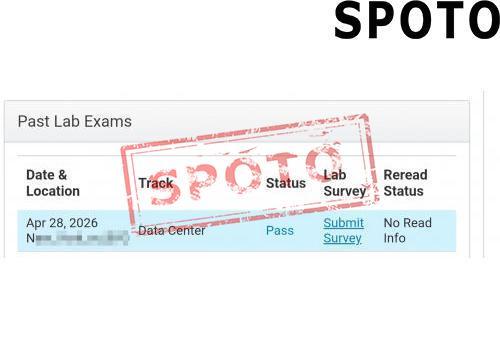
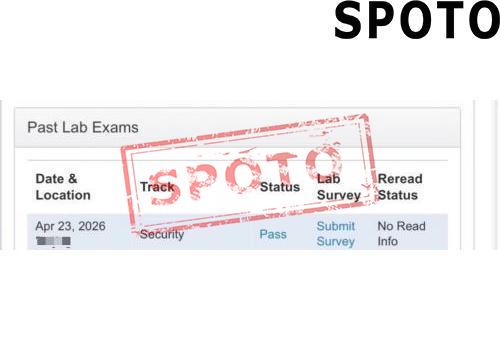
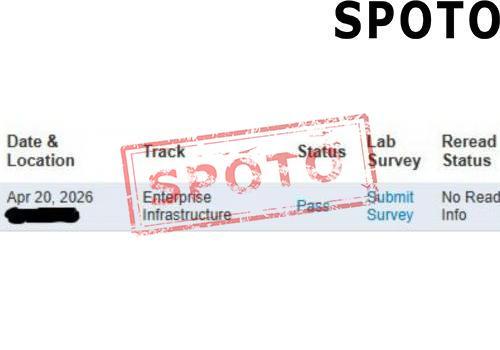
Relevance to Networking Certification Candidates
This incident directly reinforces topics examined across major Cisco certification tracks. Candidates preparing for CCNA, CCNP Enterprise, CCNP Security, and CCIE exams through platforms such as SPOTO's IT certification training resources will recognize several exam-relevant concepts embedded in this event: IOS XE architecture and management plane hardening, OSPF vulnerability surface, RESTCONF/NETCONF API security, privilege escalation vectors, and incident response procedures for network infrastructure. Understanding real-world exploitation scenarios like this one strengthens both exam readiness and practical operational competence. SPOTO's CCNP Security and CCIE Security study materials cover management plane protection, infrastructure ACLs, and control plane policing — all directly applicable to defending against the attack vectors exploited in this incident.
Sources
- Cisco Security Advisories — Cisco PSIRT (April 2026)
- CISA Alert: Cisco IOS XE Critical Vulnerabilities (April 2026) — US Cybersecurity and Infrastructure Security Agency
- UK NCSC Advisory on Cisco IOS XE Exploitation (April 2026) — National Cyber Security Centre
- Mandiant Threat Intelligence: UNC5830 Activity Linked to Cisco IOS XE Exploitation (May 2026) — Mandiant / Google Cloud
- Cisco Talos Blog: IOS XE Vulnerability Analysis and IoCs (April–May 2026) — Cisco Talos Intelligence Group
- Palo Alto Networks Unit 42: Active Exploitation of Cisco IOS XE CVEs (May 2026)
- Shodan Internet Scan Data: IOS XE Exposed Management Interfaces (May 2026)
- Global Network Communications Market 2026: AI-Driven 5G Advanced Deployments Accelerate Amid New Spectrum Policy Shifts
- Cisco Warns of Critical IOS XE Vulnerability Actively Exploited in Global Networking Infrastructure Attacks (April 2026)
- Wi-Fi 7 Adoption Surges Globally as Enterprises Race to Upgrade Network Infrastructure in 2026
- Cisco Unveils Next-Gen AI-Powered Networking Platform at Cisco Live 2026: What IT Pros Need to Know
- Wi-Fi 7 Mass Deployment Accelerates in 2026 as Global Enterprises and Carriers Race to Upgrade Network Infrastructure