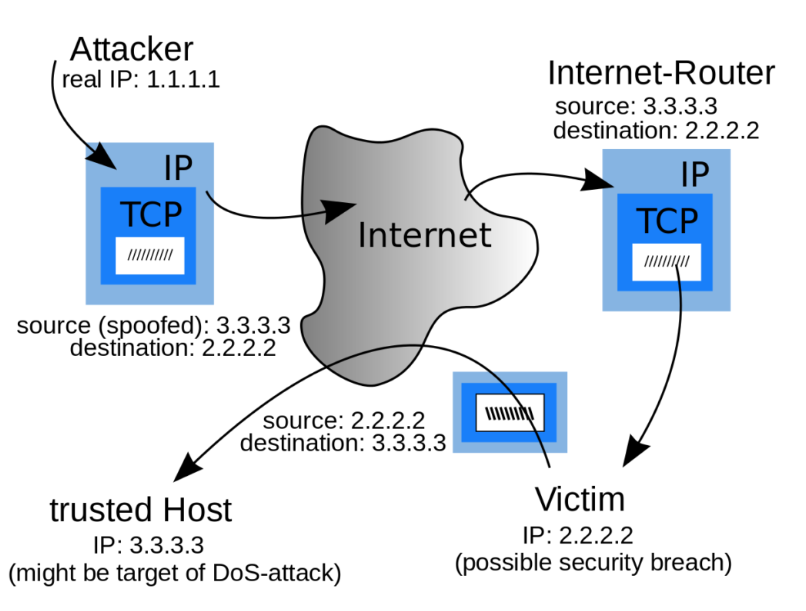
In a computer network, IP address spoofing or IP spoofing means creating a packet with an error source IP address to simulate another computing system.
The basic protocol for sending data over the Internet is an Internet Protocol (IP). This protocol specifies that each IP packet must have a header that contains a number of content and the IP address of the sender of the packet. The source IP is always the address of the sending packet, but the sender address in the header can be changed, so it will be displayed to the recipient from another source.
IP Spoofing is used to authenticate into systems that only allow a specified IP address.
For example, in a corporate network, internal systems typically trust each other so that users can log in without credentials. An attacker on the same network can access the target computer without any authentication by spoofing the trusted computer’s IP address.
IP address spoofing is mainly used in denial of service attacks, the idea is to drown the target with very high traffic, and the attacker is not concerned about receiving the response to the attack packet.
Services vulnerable to IP spoofing:
· RPC (Remote procedure call services)
· Any service that uses IP address authentication
· The X Window System
· The R services suite (rlogin, rsh, etc.)
IP Spoofing occurs at Layer 3, the network layer
IP spoofing is not a simple solution because it is inherent in the TCP/ IP suite design. Learn how and why to use spoofing attacks and combine some simple methods of prevention to help protect your network.
Notice that SPOTO will update some technical articles, and you can follow SPOTO. SPOTO is committed to the Cisco certification exams. we have real exam answers and questions. if you have any questions, and you can contact us!
More Recommended Articles
1. Types of Ethernet cables – straight-through and crossover
3. 6 Hot IT Skills You Should Gain to Discover the Internet of Things

 Join Telegram Study Group ▷
Join Telegram Study Group ▷